National Guard Cyber Warriors Prepare for Battle during Cyber Shield 19
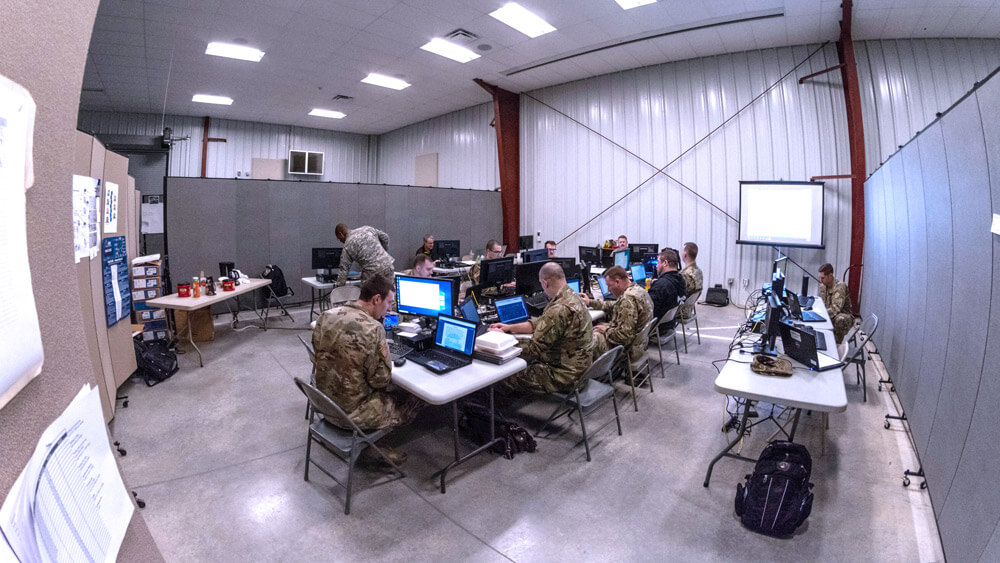
Cyber Shield 19, held in April at Camp Atterbury, Indiana, as the latest iteration of the annual Cyber Shield event series, was an Army National Guard-sponsored exercise that brought together more than 700 participants from 39 States and Territories.
Armed with keyboards, data and technical jargon, Army National Guard Soldiers took to the cyber battleground to train and test their abilities during the largest unclassified cyber exercise in the Department of Defense (DoD).

More than 500 of the participants were Army National Guard Soldiers, while the remaining participants were made up of members of the Air National Guard, Army Reserve, law enforcement community, DoD and cyber defense industry partners, which included Microsoft and CISCO.
Each year, Cyber Shield brings together U.S. Soldiers, Airmen and civilians, State and federal agencies, and industry partners to focus on exchanging best practices and testing vital cyber skills.
“The main goal of Cyber Shield is defensive cyber operations training,” said George Battistelli, the Army National Guard cybersecurity program manager, information technology strategy division chief and the Cyber Shield 19 exercise director. “It’s a training and an opportunity for participants to put their hands on keyboards and actually identify and respond to malicious events and activity.”
The exercise took place over the course of two weeks. The first week focused solely on training. Participants received hands-on cyber training that would later be tested during the second week of the exercise.
“We bring in the top instructors in the nation [for] the exercise,” explained COL Terry Williams, commander of Cyber Shield and deputy commander of the 91st Cyber Brigade. “They train our Soldiers, Airmen and service members on the latest and greatest techniques.”

The second week allows participants to put what they learned during the first week into action through a series of scenario-based exercises. In its twelfth iteration, Cyber Shield presents new scenarios, challenges and technologies every year. As cyber is an ever changing and developing field, Cyber Shield planners seek to embody that same type of constant evolution in the exercise’s challenging scenarios.
“Every year we try to diversify the scenario because it’s difficult for us to predict from what angle the threat actors may be approaching,” said MAJ Dayna Sanders, J3 of Cyber Shield 19 with the Kentucky Army National Guard’s Joint Force Headquarters. “We need to get better every year from different angles.”
Cyber Shield 19 implemented new technologies like wireless and integrated Internet Protocol version 6 (IPv6). IPv6 is the most recent version of the Internet Protocol (IP)—a communications tool that provides an identification and location system for computers on networks and routes traffic across the internet. The incorporation of new technologies such as IPv6, contributed to the selection of this year’s very timely event theme of election systems.

“We are pretty proud we were able to get elections into the scenario,” said COL Williams. “Essentially, they were preparing for [the 2020 election season].”
The election scenario allowed participants to practice their cyber skills as related to helping defense systems protect the elections process. With previous exercise scenarios focused on cyber breaches within infrastructures, Cyber Shield planners decided to make a shift and have this year’s exercise tie more to current events and ongoing concerns within the cyber field.
“Election systems have been a hot topic recently,” explained MAJ Sanders. “We want people to know that we’re paying attention, we’re training and our training is relevant. We’re working to better understand and to help our State partners to better defend our critical infrastructures, like the election system.”
Growing in reputation, Cyber Shield 19 included a higher number of participants from a larger number of organizations than previous years. This year included participants from the Coast Guard, Navy and the FBI, who performed a mock arrest of a cybercriminal.
During the exercise, Soldiers performed in specific teams based on their role in the scenario. The blue team connected with a network owner, played by an actual participating industry partner, to defend their system. The red team attacked the blue team’s systems while the white team conducted assessments of the exercise. As there was a diverse range of experience and skillsets amongst participants, the exercise incorporated three tiers of attack to effectively challenge every participant.
“We have some States that send their top team for training and some States that may send their second-tier teams to get training, depending on their rotation,” explained Battistelli. “We have the ability to tailor that training for them, and we look at it like the gas pedal method. Sometimes we’re going to push the gas pedal harder and give them deeper injects. If they’re struggling, we can ease back and give them some [easier] injects or send help from one of the other cells. That allows them to identify and eradicate much more efficiently.”
“Whatever level you were at, you were going to be challenged,” said COL Williams.
General feedback indicated that, based on the amount of knowledge and practice participants gained, the overall exercise was worthwhile and well received.
“It was an extremely successful exercise,” said SPC Kaitlyn Christian of the North Carolina Army National Guard’s 505th Engineer Battalion. “I know I personally learned so much. I’m just breaking into this field so getting the opportunity to learn from instructors during training week and learn from other individuals that do this as their full-time job was such a great opportunity.”
As a forensics cell member, SPC Christian assisted in analyzing digital evidence. She said since it was a new area of experience for her, she enjoyed the opportunity to push herself and advance her skills.
“The exercise challenged me by getting me out of my comfort zone,” SPC Christian explained. “Forensics isn’t something I’ve done before, so [it tested] me when new problems came about. I learned what systems to use to solve those problems, and the techniques and processes to go through to solve the problems that were sent to us.”
Working closely with other participants highlighted how deterring cyber threats is truly a team effort.
“I learned that when a cyber incident occurs, it’s not one person going about solving the incident,” SPC Christian went on to say. “It really takes a team and a lot of knowledge from that team to learn what happened and critically think to put the pieces together to solve the problem, figure out how to recover from that problem and mitigate future attacks.”
The opportunity to form bonds and sync with industry and State partners while gaining vital cyber expertise was also a major takeaway from the exercise.
“This exercise gives Guard Soldiers exposure to the cyber incident response, and it gets them exposure to other members that do this full-time,” explained SPC Christian. “It gives them an opportunity to learn and take back different techniques and an opportunity to network and meet individuals that you can call up when you have an issue.”
By providing excellent training and a space to showcase Soldier skills, the Cyber Shield exercise proved to once again highlight the vital role Cyber Soldiers play in cyber defense.
“I truly believe that Cyber Guard members are national treasures for the future code wars,” said COL Williams. “I think they really bring a lot to the table in the sense that they are out in the civilian sector, they all see a plethora of different attacks and different technologies. Then you bring them all together and all that knowledge is residing in one area for two weeks. It’s amazing what they walk away with.”
BY STAFF WRITER Tatyana White-Jenkins


